Build sophisticated apps with role-based security and track every single action made with your workflows. Logiforms offers advanced security features to comply with PIPEDA, HIPAA , PCI and GDPR.
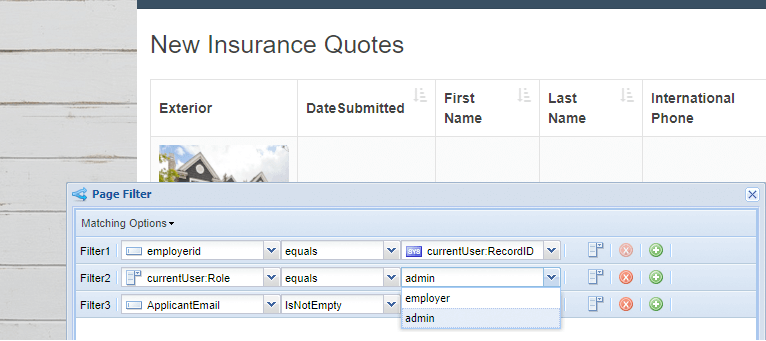
Role-Based Security
Everything within your workflow can be filtered and conditional based on the logged in users role. Hide data pages, columns, and actions based on the logged in users roles. It's simple and easy to set up. This easy to use role-based security system makes it a breeze to filter data to show only the data that belongs to the currently logged in user, or only show admin controls to users in the admin role.
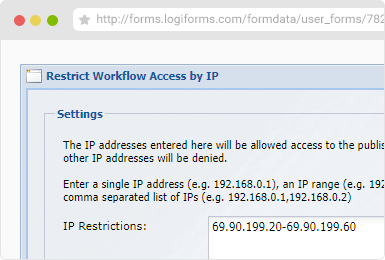
IP Based Security
Restrict access to your workflows to only your network via an IP, a range or a list of IP addresses. Use in conjunction with encryption, strong password policies and form IP security to create a robust security framework.
Auditing and Tracking
Every single action taken with your workflows by logged in users is tracked and recorded. You can view what pages they viewed and any actions they've taken. All updates made to your data is also tracked and can be accessed via the audit log, or use our comparison tools to view a DIFF view history of every single field of data in your database.
